How Malicious Android Apps Slip Into Disguise

Mobile malware vendors are exploiting a flaw in Google's Android platform that allows them to hide malicious code in mobile apps and bypass security screening tools, researchers say. Google says it has updated its app's malware detection methods in response to the new research.
Researchers at Amsterdam-based security firm ThreatFabrik have discovered a mobile malware penetration technique. Alexander Eremin , the company's chief malware analyst, told KrebsOnSecurity that they recently came across a number of mobile banking Trojans that exploit a bug in all versions of the Android operating system. Popular mobile security scanning tools, the software is completely reliable and successfully installed on Android OS.
"There is malware that compresses the .apk [app installation file] so that the platform still considers it valid and performs all the malicious activities it was designed for, but many devices cannot run that code," Yermin explained.
Yeremin said ThreatFabric has seen this malware attack technology used many times in the past, but in April 2023, it began detecting several types of mobile malware families that use it for privacy. The company achieved this breakthrough in part by offering automated malware as a covert service to cybercriminals that hides or "disguises" malicious mobile apps for a fee.
Yeremin Google marked the first report of May 9, 2023 as "high". Google recently offered a $5,000 reward for finding the bug, even though its discovery isn't technically a security vulnerability.
"This discovered issue was not classified as a security vulnerability and did not affect the Android Open Source Project (AOSP), but it prompted us to update our malware detection strategies for apps that may try to exploit this vulnerability," Google said in a statement. .
Google acknowledges that some of the tools it provides to developers, including APK Analyzer, cannot currently be used to analyze malware and consider it safe by allowing it to be installed on users' devices.
"We are investigating potential fixes for the developer tools and plan to update our documentation accordingly," Google said in a statement.
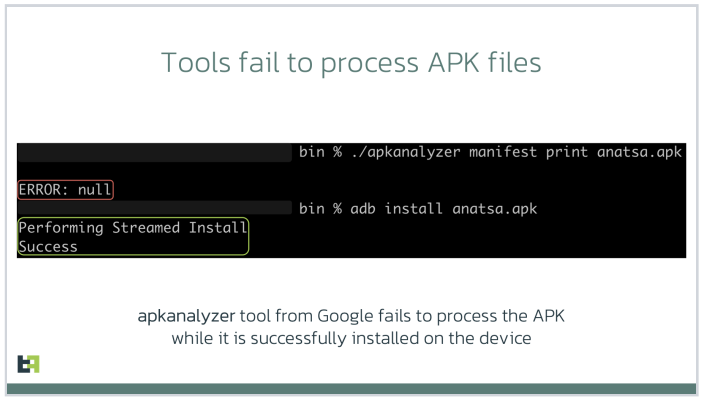
Photo: ThreatFabric.
According to ThreatFabric, software analysts can find several signs that malware is exploiting a vulnerability. First, they found that apps updated in this way had more Android reflection files containing new schemas than other files in the app bundle.
More importantly, the documentation file itself is modified so that the number of "lines" specified in the program—clear text in the code, like comments—matches the actual number of lines in the program.
One mobile malware using this trick is known as Minority , which is a sophisticated Android banking Trojan that is usually a good file manager app. Last month, ThreatFabric revealed that the scammers behind the minority are buying outdated abandoned file-management apps or building their own, allowing them to build up a large user base before the app is updated with malicious components.
ThreatFabric reports that Anatsa works like a PDF viewer and other file management software because such software has the right to delete or modify other files already on the host machine. The company estimates that the people behind Minority have delivered more than 30,000 installs of their banking Trojans to the Google Play Store as part of ongoing malware campaigns.
In recent months, the Google Play Store has been criticized for not keeping a close eye on malware or legitimate apps that are later found to be illegal. A May 2023 article from Ars Technica claims that when Google discovered a previously questionable screen recording app on its platform that infected 50,000 users, the company removed it, as well as thanking the third-party researchers who found it. actually. Malware, no comments. As soon as he heard it.
“The company explained why researchers and the automated scanning process did not overlook malware detected by outsiders,” Ars Dan Godin wrote. Google also refrains from proactively notifying Play users once it becomes aware of their participation in the Service.
The Ars article mentions a recent change at Google that could be positive: a countermeasure available in Android 11 and later is "app snooze," which puts apps to sleep and revokes previously granted launch permissions.


