Thousands Of Android APKs Use Compression Trick To Thwart Analysis

Attackers are increasingly distributing malicious Android APKs (bundled app installers) that prevent decompilation using unsupported, unknown, or carefully optimized compression algorithms.
The main benefit of this approach is that it avoids detection by security tools through static analysis and makes it more difficult for researchers to investigate, delaying the development of a deeper understanding of how Android malware strains work. .
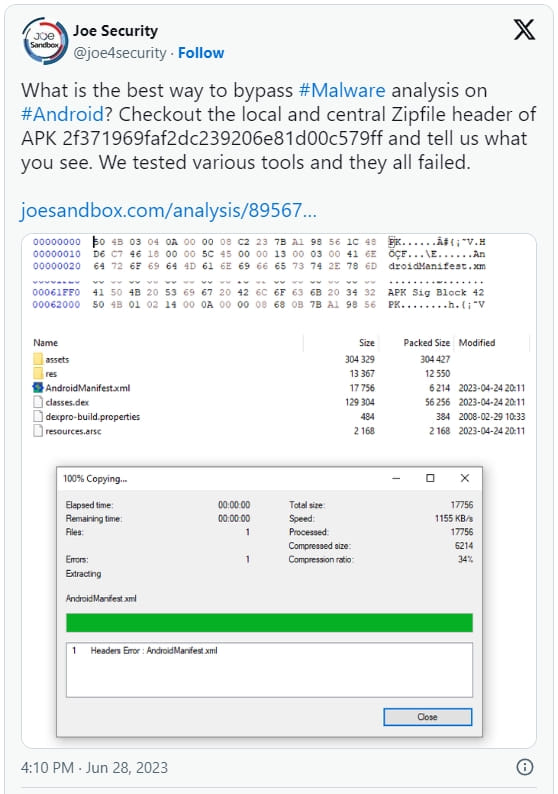
Zimperium, a member of the App Defense Alliance that detects and removes Google Play malware, investigated the decompile resistance situation after Joe Security tweeted an APK that couldn't be parsed but worked perfectly on Android devices.
A zLab report published yesterday claims that 3,300 APKs use these unusual scanning protection methods, causing many of them to fail. However, researchers have found a subset of 71 malicious APKs that work perfectly on Android version 9 (API 28) and higher.
Zimperium makes it clear that none of these apps are in the Google Play Store, but lists their hashes at the bottom of the report to help people find and remove apps from third-party stores.
The Android APK uses the ZIP format in two modes, one without compression and one that uses the deflation algorithm.
APK files compressed with unsupported or unknown compression methods cannot be installed on Android 8 and earlier, but will work fine on Android 9 and later.
Zimperium tested samples taken with the JADX, APKtool, and macOS Archive Utility unpacking tools, and none of them were able to unpack the APK for analysis.
In addition to using unsupported compression methods, Zimperium also discovered that malicious APK authors use file names longer than 256 bytes to shut down analysis tools, obfuscate the AndroidManifest.xml file, and use bad string pools to shut down the tool. Android XML File Sharing.
These are all anti-scan methods, and while Gimperium does not go into detail about what exactly these malicious APKs do, their intention to hide their functionality is unlikely to be harmless.
Since APK files downloaded from outside of Google Play cannot be verified, the best way to protect yourself from these threats is to avoid installing Android apps from third-party sites in the first place.
If you want to install a non-Google Play app, please scan it before installing with a reputable mobile antivirus tool.
When installing the program, pay attention to the requested permissions and look for warning signs that are not related to the main functions of the program.
Finally, "rooting" your Android device makes the user an administrator, allowing you to run malicious APKs with full privileges on the operating system, so it is generally not recommended.


